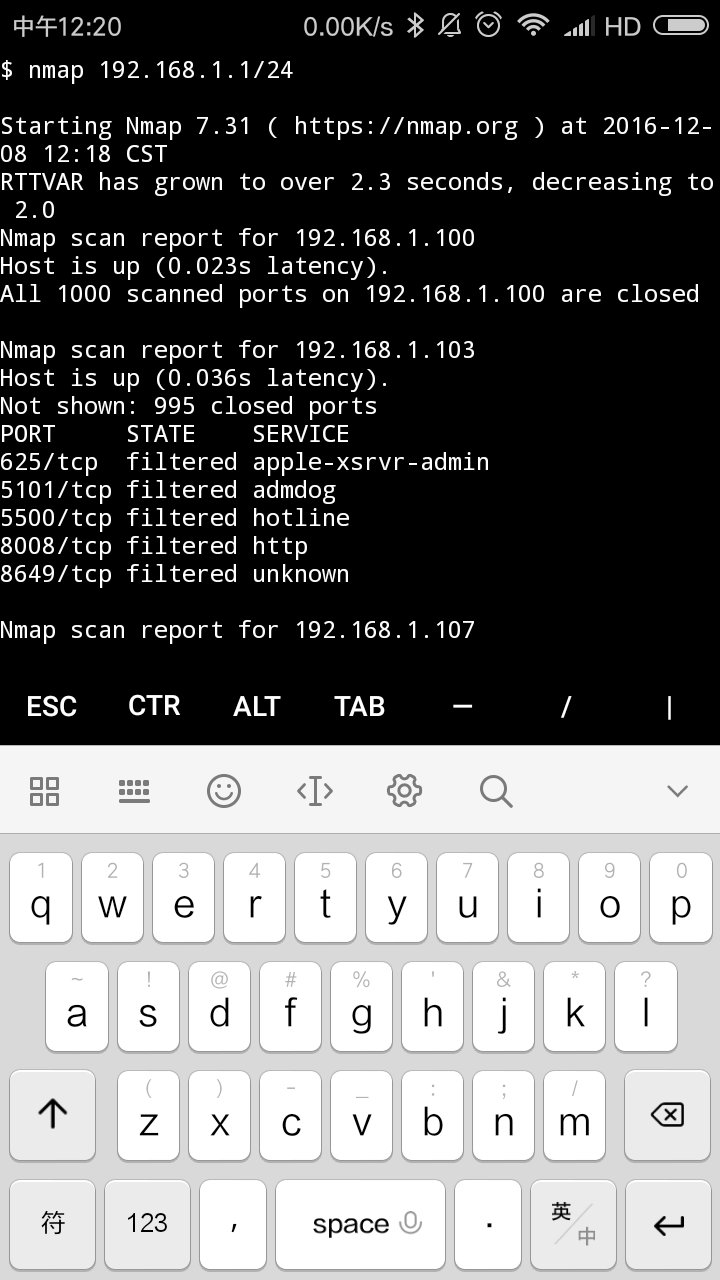
Installing Nmap on Android Termux grants access to a powerful network scanner within the Android environment. Nmap (Network Mapper) is an open-source tool designed for comprehensive network exploration and security auditing. By leveraging Nmap's capabilities on Android Termux, users can conduct network reconnaissance, identify open ports, and assess system vulnerabilities, making it invaluable for security professionals, network administrators, and ethical hackers.
To embark on installing Nmap within Termux, commence by updating the package repositories:
apt updateSubsequently, proceed with installing Nmap:
apt install nmapOnce the installation culminates, verify the successful installation:
nmap --versionThis command should yield an output displaying the installed Nmap version, signifying a successful installation.
Harnessing Nmap on Android Termux unlocks a plethora of network analysis possibilities. Security professionals can leverage Nmap to uncover vulnerabilities within their networks, while network administrators can utilize it to monitor network traffic and pinpoint potential issues. Ethical hackers can employ Nmap to uncover exploitable entry points, bolstering their offensive security skillset.
How to Install Nmap in Android Termux
Installing Nmap in Android Termux opens up a world of network exploration and analysis possibilities. Here are 10 key aspects to consider:
- Package Management: Utilize Termux's package management system for seamless installation.
- Command-Line Interface: Interact with Nmap through the command line for advanced control.
- Network Scanning: Perform comprehensive scans to identify hosts, ports, and services.
- Vulnerability Assessment: Uncover potential vulnerabilities within networks.
- Security Auditing: Conduct thorough security audits to enhance network resilience.
- Port Analysis: Determine open ports and their associated services.
- Host Discovery: Identify and enumerate hosts within a network.
- Network Monitoring: Monitor network traffic and identify anomalies.
- Ethical Hacking: Leverage Nmap for ethical hacking and penetration testing.
- Cross-Platform Compatibility: Nmap runs seamlessly on Android Termux, providing cross-platform consistency.
These aspects collectively make Nmap an indispensable tool for network professionals, security researchers, and ethical hackers. Its ability to perform comprehensive network scans, uncover vulnerabilities, and aid in security audits makes it a cornerstone of network analysis and security assessment.
Package Management
Within the context of "how to install nmap in android termux", package management plays a pivotal role in simplifying the installation process. Termux employs a package management system that streamlines software installation and updates, akin to package managers found in desktop operating systems. This mechanism alleviates the need for manual compilation or complex dependency resolution, making Nmap installation as straightforward as issuing a single command.
- Package Repository: Termux maintains a comprehensive repository of pre-compiled packages, including Nmap. This repository serves as a central source for software, ensuring authenticity and integrity during installation.
- Dependency Management: Nmap, like many software applications, relies on other software components (dependencies) to function correctly. Termux's package management system automatically resolves and installs these dependencies, ensuring a seamless installation process.
- Version Control: The package management system keeps track of installed software versions. This allows for effortless updates to newer versions of Nmap or its dependencies, ensuring access to the latest features and security patches.
- Package Removal: Should the need arise to remove Nmap or any other installed package, the package management system provides a streamlined uninstallation process. This ensures proper cleanup and frees up storage space.
In summary, Termux's package management system streamlines the installation and management of Nmap and other software packages. It simplifies the process, ensures dependency resolution, facilitates updates, and enables easy removal when necessary, making it an integral aspect of "how to install nmap in android termux".
Command-Line Interface
The command-line interface (CLI) is an essential component of "how to install nmap in android termux" as it provides advanced control and flexibility in the installation and usage of Nmap. Unlike graphical user interfaces (GUIs), which often simplify tasks with pre-defined options, the CLI grants direct access to the full range of Nmap's capabilities. This enables users to tailor Nmap's behavior precisely, adapting it to their specific needs and scenarios.
The CLI allows users to specify intricate scan parameters, such as target IP addresses, port ranges, and specific scan types. This level of granularity is crucial for thorough and targeted network analysis. Additionally, the CLI facilitates the automation of Nmap tasks through scripts and batch files, enabling repetitive or complex scans to be executed efficiently.
Moreover, the CLI serves as a gateway to Nmap's advanced features, such as NSE (Nmap Scripting Engine) scripts. These scripts extend Nmap's functionality, enabling users to perform specialized tasks like vulnerability detection, service fingerprinting, and web application scanning. The CLI provides a direct interface to configure and execute these scripts, empowering users to deeply probe networks and uncover potential security risks.
In summary, the command-line interface is a critical aspect of "how to install nmap in android termux" as it grants advanced control, flexibility, and access to Nmap's full capabilities. It empowers users to conduct tailored scans, automate tasks, and leverage NSE scripts, making it indispensable for network analysts, security professionals, and ethical hackers alike.
Network Scanning
Network scanning lies at the core of "how to install nmap in android termux" as it establishes the foundation for network analysis and security assessment. Nmap's robust scanning capabilities allow users to identify hosts, open ports, and running services within a network, providing critical insights into its topology and potential vulnerabilities.
Network scanning is essential for various reasons. Firstly, it enables the discovery of hosts within a network, creating an inventory of connected devices. This information is crucial for network administrators to track assets, manage IP address assignments, and identify unauthorized devices. Secondly, port scanning reveals which ports are open on each host, indicating the services running on those systems. This knowledge is vital for assessing the attack surface of a network and identifying potential entry points for attackers.
Furthermore, service scanning provides detailed information about the services running on open ports. Nmap can identify the specific applications and versions running on each service, enabling administrators to determine if they are up-to-date and secure. This information is particularly valuable for vulnerability management and intrusion detection.
In summary, network scanning is an indispensable component of "how to install nmap in android termux" as it provides the foundational knowledge necessary for effective network management, security assessment, and threat mitigation. By identifying hosts, ports, and services, Nmap empowers users to gain a comprehensive understanding of their network infrastructure and proactively address potential security risks.
Vulnerability Assessment
Vulnerability assessment forms an integral part of "how to install nmap in android termux" as it empowers users to identify and address security weaknesses within their networks. Nmap's advanced scanning capabilities provide a comprehensive overview of network vulnerabilities, enabling proactive remediation and enhanced security posture.
- Network Discovery: Nmap's network scanning features allow users to discover all devices connected to a network, including servers, workstations, and IoT devices. This comprehensive inventory is essential for vulnerability assessment as it ensures that no assets are overlooked.
- Port and Service Identification: Nmap can identify open ports and running services on each discovered device. This information is crucial for vulnerability assessment as it reveals potential entry points for attackers and helps prioritize remediation efforts.
- Vulnerability Detection: Nmap integrates with various vulnerability databases and provides real-time vulnerability detection. It cross-references the identified services and versions against known vulnerabilities, highlighting potential security risks.
- Exploit Detection: Nmap's NSE (Nmap Scripting Engine) scripts enable the detection of specific exploits and vulnerabilities. These scripts simulate real-world attack techniques, providing valuable insights into the potential impact of vulnerabilities.
In summary, vulnerability assessment is a critical aspect of "how to install nmap in android termux" as it provides a comprehensive understanding of network vulnerabilities. By leveraging Nmap's advanced scanning and detection capabilities, users can proactively identify and remediate security weaknesses, minimizing the risk of successful attacks and enhancing the overall security posture of their networks.
Security Auditing
Security auditing plays a crucial role in "how to install nmap in android termux" by empowering users to conduct comprehensive security assessments of their networks, identifying vulnerabilities, and implementing measures to enhance resilience against cyber threats.
- Network Vulnerability Assessment: Nmap's advanced scanning capabilities enable auditors to identify open ports, running services, and potential vulnerabilities within a network. This information is critical for understanding the attack surface and prioritizing remediation efforts.
- Configuration Review: Security audits involve reviewing network configurations, including firewall rules, access control lists, and security policies. Nmap can assist in identifying misconfigurations that could lead to security breaches.
- Compliance Verification: Organizations subject to regulatory compliance standards can leverage Nmap to verify adherence to security requirements. Nmap's auditing capabilities can generate reports that demonstrate compliance with industry best practices and regulations.
- Penetration Testing: Nmap's NSE scripts provide the ability to simulate real-world attacks, allowing auditors to test the effectiveness of security controls and identify potential vulnerabilities that could be exploited by malicious actors.
In summary, security auditing is a vital aspect of "how to install nmap in android termux" as it enables users to proactively identify and address security risks, ensuring the confidentiality, integrity, and availability of their networks.
Port Analysis
Port analysis is a crucial component of "how to install nmap in android termux" as it provides deep insights into the services running on a network, enabling effective network management, security assessment, and troubleshooting.
Open ports are potential entry points for both legitimate and malicious traffic. Identifying and understanding the services associated with these ports is essential for making informed decisions about firewall configurations, access control policies, and intrusion prevention measures.
For instance, if a port scan reveals that port 22 (SSH) is open on a server, the administrator knows that SSH services are available on that server. This information can be used to configure firewall rules to restrict access to SSH only from authorized IP addresses, reducing the risk of unauthorized access.
Furthermore, port analysis aids in troubleshooting network connectivity issues. By identifying which ports are open or closed on a particular device, network administrators can pinpoint the source of connectivity problems and take appropriate action.
In summary, port analysis is an indispensable aspect of "how to install nmap in android termux" as it empowers users to understand the services running on their networks, make informed security decisions, and troubleshoot connectivity issues, contributing significantly to the overall security and efficiency of network operations.
Host Discovery
Host discovery forms a critical foundation for "how to install nmap in android termux" as it provides a comprehensive understanding of the network landscape, including the identification and enumeration of all hosts connected to the network.
Accurately identifying and enumerating hosts is essential for several reasons. Firstly, it establishes a baseline for network management, enabling administrators to track assets, manage IP address assignments, and monitor network usage. Secondly, host discovery is crucial for security assessment as it uncovers potential entry points for unauthorized access and helps prioritize vulnerability management efforts.
For instance, in a corporate network, host discovery can reveal the presence of rogue devices or unauthorized servers that may pose security risks. By identifying and enumerating all hosts, administrators can proactively address security vulnerabilities and maintain a secure network environment.
Furthermore, host discovery plays a vital role in network troubleshooting. By identifying all active hosts on a network, administrators can pinpoint the source of connectivity issues and take appropriate action to resolve them. This is particularly valuable in large and complex networks where identifying the root cause of connectivity problems can be challenging.
In summary, host discovery is an indispensable component of "how to install nmap in android termux" as it provides essential information for network management, security assessment, and troubleshooting. By accurately identifying and enumerating all hosts within a network, Nmap empowers users to gain a comprehensive understanding of their network infrastructure and proactively address potential security risks.
Network Monitoring
Network monitoring is an integral aspect of "how to install nmap in android termux" as it provides real-time visibility into network traffic, enabling the detection and identification of anomalies that may indicate security breaches or performance issues.
Nmap's advanced packet capture and analysis capabilities empower users to monitor network traffic, analyze packet headers, and identify patterns that deviate from normal network behavior. This information is critical for security teams to detect and respond to malicious activities, such as unauthorized access attempts, data exfiltration, or denial-of-service attacks.
For instance, an Nmap-based network monitoring system can be configured to monitor traffic for unusual traffic patterns, such as sudden spikes in traffic volume or the presence of specific attack signatures. By identifying these anomalies, security teams can quickly investigate and take appropriate action to mitigate potential threats.
Furthermore, network monitoring is essential for maintaining optimal network performance. By analyzing traffic patterns, administrators can identify bottlenecks, optimize bandwidth utilization, and troubleshoot connectivity issues. This proactive approach helps prevent network outages and ensures the smooth flow of critical business applications.
In summary, network monitoring is a crucial component of "how to install nmap in android termux" as it enables the detection of security breaches, optimization of network performance, and proactive troubleshooting. By leveraging Nmap's advanced traffic analysis capabilities, users can gain deep insights into their network traffic, identify anomalies, and take timely action to maintain a secure and efficient network environment.
Ethical Hacking
Within the realm of "how to install nmap in android termux," the connection to ethical hacking and penetration testing holds significant relevance. Ethical hackers and penetration testers utilize Nmap as a cornerstone tool for uncovering vulnerabilities and assessing network security.
- Vulnerability Assessment: Nmap empowers ethical hackers to conduct comprehensive vulnerability assessments, identifying potential weaknesses in networks and systems. By simulating real-world attacks, Nmap helps ethical hackers prioritize remediation efforts and enhance overall security posture.
- Network Reconnaissance: Ethical hackers leverage Nmap's reconnaissance capabilities to gather detailed information about target networks, including host discovery, port scanning, and service identification. This reconnaissance phase lays the groundwork for subsequent penetration testing activities.
- Exploit Verification: Nmap's NSE scripts provide a repository of exploit verification scripts, enabling ethical hackers to test and verify the effectiveness of known vulnerabilities. This verification process ensures that identified vulnerabilities are genuine and pose a legitimate risk.
- Penetration Testing: Nmap plays a crucial role in penetration testing, allowing ethical hackers to simulate real-world attacks and assess the resilience of target systems. By launching targeted attacks against specific vulnerabilities, ethical hackers can identify potential entry points and mitigate risks.
In conclusion, the connection between "Ethical Hacking: Leverage Nmap for ethical hacking and penetration testing" and "how to install nmap in android termux" underscores the critical role of Nmap in ethical hacking practices. By empowering ethical hackers with advanced scanning and exploitation capabilities, Nmap contributes significantly to enhancing network security and safeguarding systems from malicious actors.
Cross-Platform Compatibility
Within the context of "how to install nmap in android termux," the cross-platform compatibility of Nmap on Android Termux holds significant relevance and offers several advantages.
- Universal Accessibility: Nmap's availability on Android Termux extends its accessibility to a wide range of devices, including smartphones and tablets, empowering users to perform network analysis and security assessments on the go.
- Standardized Functionality: Regardless of the underlying hardware or operating system, Nmap on Android Termux maintains consistent functionality and behavior. This standardization ensures that users can rely on a familiar and reliable toolset across different platforms.
- Simplified Deployment: The cross-platform compatibility of Nmap on Android Termux simplifies deployment and maintenance. System administrators and security professionals can easily install and use Nmap on Android Termux without the need for complex configuration or compatibility concerns.
- Ubiquitous Knowledge Base: The cross-platform consistency of Nmap on Android Termux fosters a unified knowledge base and community support. Users can leverage resources, tutorials, and discussions applicable to Nmap across different platforms, enhancing their learning and troubleshooting capabilities.
In summary, the cross-platform compatibility of Nmap on Android Termux contributes to the accessibility, standardization, simplified deployment, and ubiquitous knowledge base of Nmap, making it an indispensable tool for network analysis and security assessments in diverse environments.
Frequently Asked Questions about "How to Install Nmap in Android Termux"
This section addresses common questions and misconceptions regarding the installation and usage of Nmap on Android Termux.
Question 1: What are the prerequisites for installing Nmap on Android Termux?
To successfully install Nmap on Android Termux, you will need an Android device running Android 5.0 or later and the Termux app installed.
Question 2: Is Nmap available for free on Android Termux?
Yes, Nmap is open-source software and is available for free on Android Termux. You can install it without any licensing fees.
Question 3: Can I use Nmap on Android Termux to scan remote networks?
Yes, Nmap on Android Termux allows you to perform network scans on remote networks. However, ensure you have the necessary permissions and comply with ethical hacking guidelines.
Question 4: Are there any limitations to using Nmap on Android Termux compared to using it on a desktop operating system?
While Nmap on Android Termux provides comprehensive functionality, there may be some limitations compared to a desktop environment. For instance, the processing power and memory available on an Android device may affect the speed and scale of certain scans.
Question 5: What are some common use cases for Nmap on Android Termux?
Nmap on Android Termux finds applications in various scenarios, including network discovery, port scanning, vulnerability assessment, and security auditing.
Question 6: Where can I find additional resources and support for using Nmap on Android Termux?
There are numerous online forums, documentation, and tutorials available to assist you. Additionally, the Nmap community is active and provides support through various channels.
These FAQs provide a concise overview of common queries related to "How to Install Nmap in Android Termux." Refer to the official Nmap documentation and community resources for more in-depth information.
Now that you have a better understanding of installing and using Nmap on Android Termux, you can harness its capabilities to enhance your network analysis and security assessment skills.
Tips for Installing and Using Nmap in Android Termux
Harness the full potential of Nmap on Android Termux by implementing these practical tips:
Tip 1: Leverage Advanced Scanning Techniques: Employ Nmap's diverse scan types to gather comprehensive network information. Utilize techniques like SYN scans, UDP scans, and OS detection to identify open ports, running services, and operating systems.
Tip 2: Utilize NSE Scripts for Extended Functionality: Enhance Nmap's capabilities by integrating NSE scripts. These scripts offer specialized functions such as vulnerability detection, web application scanning, and exploitation verification, empowering you with deep insights into network security.
Tip 3: Master Command-Line Proficiency: Gain proficiency in Nmap's command-line interface. This provides granular control over scans, allowing you to tailor parameters, automate tasks, and delve into advanced features.
Tip 4: Prioritize Network Security: Utilize Nmap for proactive network security assessments. Conduct regular scans to identify vulnerabilities and misconfigurations, enabling timely remediation and mitigation of potential threats.
Tip 5: Adhere to Ethical Hacking Guidelines: When conducting scans, adhere to ethical hacking principles. Obtain necessary permissions, respect privacy laws, and avoid malicious activities. Use Nmap responsibly for authorized security assessments and vulnerability discovery.
Tip 6: Stay Updated with Nmap Releases: Keep abreast of the latest Nmap releases to benefit from new features and security enhancements. Regularly check the official Nmap website for updates and incorporate them into your toolkit.
Tip 7: Explore Online Resources and Community Support: Engage with the active Nmap community through online forums and documentation. Seek assistance, share knowledge, and contribute to the collective understanding of Nmap's capabilities.
By incorporating these tips, you can maximize the effectiveness of Nmap on Android Termux, empowering you to conduct thorough network analysis, enhance security posture, and advance your ethical hacking skills.
Conclusion
In conclusion, installing Nmap on Android Termux unlocks a powerful toolset for network analysis and security assessment within the Android environment. This comprehensive guide has explored the significance, installation process, and diverse applications of Nmap on Android Termux, empowering you to leverage its capabilities effectively.
By mastering the techniques and tips outlined in this article, you can harness Nmap's full potential to conduct thorough network scans, uncover vulnerabilities, and enhance the security posture of your networks. As technology continues to evolve, Nmap remains an indispensable tool for network professionals, security researchers, and ethical hackers alike.
Unveiling The Love Story: Tasha McCauley And Joseph Gordon's Enduring Bond
Unveiling Rey Mysterio's Wife: Secrets And Surprises Revealed!
Unveiling The True Self: Mika Minio Paluello's Transgender Journey
How to Install Nmap on Android using Termux 2022 (No Root)
基于Termux打造Android手机渗透神器(2017722更新) BlackWolf
ncG1vNJzZmibn6KudnrApqpsZpSetKrAwKWmnJ2Ro8CxrcKeqmebn6J8qbvWZquoZZmjwLWty6Vkp6WRpXqquoyapZ2qn56xbsDEq6SusF6dwa64